Writing policies and procedures can seem like a daunting task, yet policies can be used as a very effective tool in helping to communicate the mission, values, and guiding principles of an organization.
Here are three things to considered when writing a policy:
1. Focus of the policy
2. Lifecycle of the policy
3. The structure of policy
Policies should focus on compliance by design, where the desired behavior of incorporating cybersecurity best practices is woven into the culture of the organization. Developing comprehensive security policies include understanding the business values, legal and compliance implications, and security program design. Other things to consider would be business values, legal and compliance implications, and security program design.
It is important to understand that creating security policies is really part of a lifecycle process. Here are several steps in the life cycle of a policy.
1. Develop: Initial draft and revisions of the policy for ratification
2. Socialize: Distribution of the polices
3. Measure: Ongoing effort to review compliance to policies and to provide an enforcement mechanism to change behavior when gaps are recognized.
4. Assess: The process of reviewing policies as internal processes evolve, technology changes, or new threats expose the organization to additional risk that need to be managed.
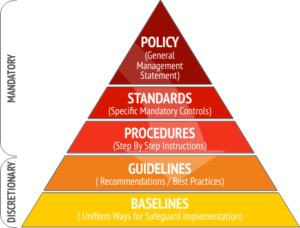
Once the focus and lifecycle has been identified, the next critical part of creating a good policy is the taxonomy of it. You want to make sure each policy is well-structured. Start with a good foundation and lay out the baselines and guidelines, then proceed to procedures, standards and policy.
Apart from the aforementioned tips, the last tip to consider is to write S.M.A.R.T policies. Make sure that the policy at the end of it is specific, measurable, achievable, relevant and time-bound.